An advanced strain of malware masquerading as a cryptocurrency miner has managed to fly the radar for over five years, infecting no less than one million devices around the world in the process.
That’s according to findings from Kaspersky, which has codenamed the threat StripedFly, describing it as an “intricate modular framework that supports both Linux and Windows.”
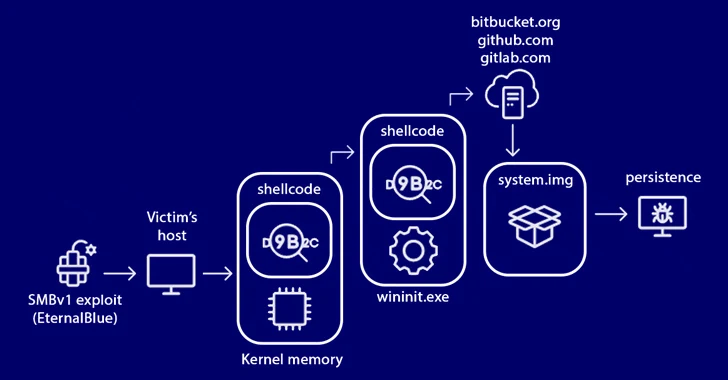
The Russian cybersecurity vendor, which first detected the samples in 2017, said the miner is part of a much larger entity that employs a custom EternalBlue SMBv1 exploit attributed to the Equation Group in order to infiltrate publicly-accessible systems.
The malicious shellcode, delivered via the exploit, has the ability to download binary files from a remote Bitbucket repository as well as execute PowerShell scripts. It also supports a collection of plugin-like expandable features to harvest sensitive data and even uninstall itself.
The platform’s shellcode is injected in the wininit.exe process, a legitimate Windows process that’s started by the boot manager (BOOTMGR) and handles the initialization of various services.
“The malware payload itself is structured as a monolithic binary executable code designed to support pluggable modules to extend or update its functionality,” security researchers Sergey Belov, Vilen Kamalov, and Sergey Lozhkin said in a technical report published last week.
“It comes equipped with a built-in TOR network tunnel for communication with command servers, along with update and delivery functionality through trusted services such as GitLab, GitHub, and Bitbucket, all using custom encrypted archives.”
Other notable spy modules allow it to gather credentials every two hours, capture screenshots on the victim’s device without detection, record microphone input, and start a reverse proxy to execute remote actions.
Upon gaining a successful foothold, the malware proceeds to disable the SMBv1 protocol on the infected host and propagate the malware to other machines using an worming module via both SMB and SSH, using keys harvested on the hacked systems.
StripedFly achieves persistence by either modifying the Windows Registry or by creating task scheduler entries if the PowerShell interpreter is installed and administrative access is available. On Linux, persistence is accomplished by means of a systemd user service, autostarted .desktop file, or by modifying /etc/rc*, profile, bashrc, or inittab files.
Also downloaded is a Monero cryptocurrency miner that leverages DNS over HTTPS (DoH) requests to resolve the pool servers, adding an extra layer of stealth to the malicious activities. It has been assessed that the miner is used as a decoy to prevent security software from discovering the full extent of the malware’s capabilities.
In an effort to minimize the footprint, malware components that can be offloaded are hosted as encrypted binaries on various code repository hosting services such as Bitbucket, GitHub, or GitLab.
For instance, the Bitbucket repository operated by the threat actor since June 2018 includes executable files capable of serving the initial infection payload across both Windows and Linux, checking for new updates, and ultimately updating the malware.
Communication with the command-and-control (C2) server, which is hosted in the TOR network, takes place using a custom, lightweight implementation of a TOR client that is not based on any publicly documented methods.
“The level of dedication demonstrated by this functionality is remarkable,” the researchers said. “The goal of hiding the C2 server at all costs drove the development of a unique and time-consuming project – the creation of its own TOR client.”
Another striking characteristic is that these repositories act as fallback mechanisms for the malware to download the update files when its primary source (i.e., the C2 server) becomes unresponsive.
Kaspersky said it further uncovered a ransomware family called ThunderCrypt that shares significant source code overlaps with StripedFly barring the absence of the SMBv1 infection module. ThunderCrypt is said to have been used against targets in Taiwan in 2017.
The origins of StripedFly remain presently unknown, although the sophistication of the framework and its parallels to EternalBlue exhibit all the hallmarks of an advanced persistent threat (APT) actor.
It’s worth pointing out that while the Shadow Brokers’ leak of the EternalBlue exploit took place on April 14, 2017, the earliest identified version of StripedFly incorporating EternalBlue dates a year back to April 9, 2016. Since the leak, the EternalBlue exploit has been repurposed by North Korean and Russian hacking outfits to spread the WannaCry and Petya malware.
That said, there’s also evidence that Chinese hacking groups may have had access to some of the Equation Group’s exploits before they were leaked online, as disclosed by Check Point in February 2021.
The similarities to malware associated with the Equation group, Kaspersky said, is also reflected in the coding style and practices resembling those seen in STRAITBIZARRE (SBZ), another cyber espionage platform wielded by the suspected U.S.-linked adversarial collective.
The development comes nearly two years after researchers from China’s Pangu Lab detailed a “top-tier” backdoor called Bvp47 that was allegedly put to use by the Equation Group on more than 287 targets spanning multiple sectors in 45 countries.
Needless to say, a crucial aspect of the campaign that continues to be a mystery – other than to those who engineered the malware – is its real purpose.
“While ThunderCrypt ransomware suggests a commercial motive for its authors, it raises the question of why they didn’t opt for the potentially more lucrative path instead,” the researchers said.
“It’s difficult to accept the notion that such sophisticated and professionally designed malware would serve such a trivial purpose, given all the evidence to the contrary.”



Leave a Reply