The E.D.A Blog
Our official blog with news, technology advice, and business culture.

Real-Time Inventory & Stock Management for POS Kenya Businesses
Real-Time Inventory & Stock Management with POS Kenya | E.D.A by Exotic Digital Access E.D.A by Exotic Digital Access · POS Kenya Real-Time Inventory &

POS Kenya for Modern Retail and Wholesale Businesses
POS Kenya — Best POS System for Retail, Wholesale & SMEs | E.D.A by Exotic Digital Access E.D.A by Exotic Digital Access · Kenya The
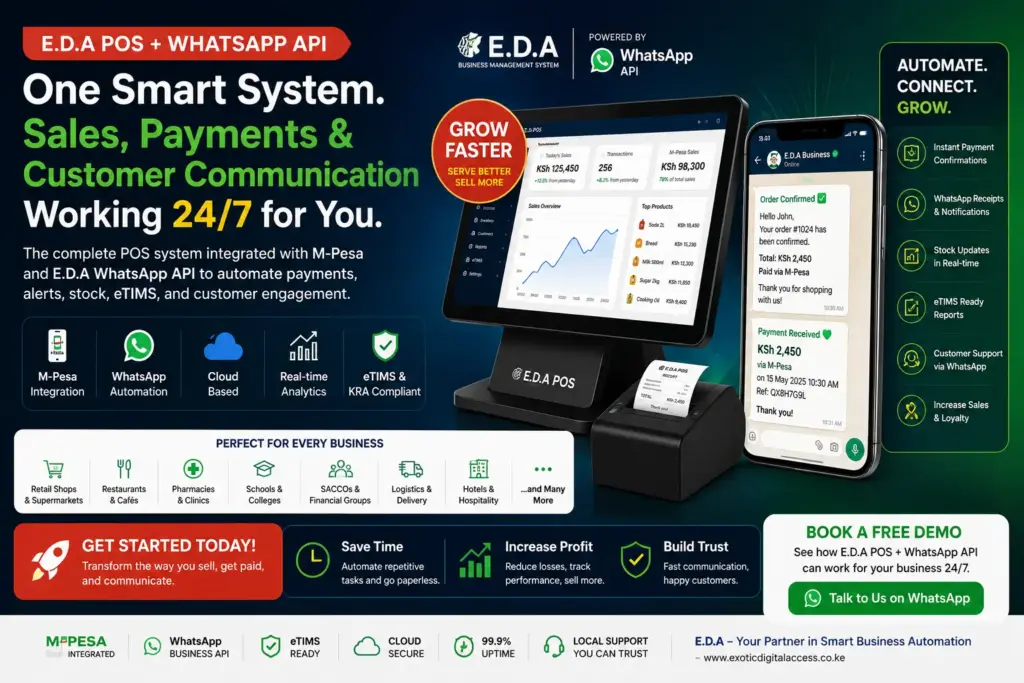
Imagine a POS System Integrated with M-Pesa and E.D.A WhatsApp API Working for You 24/7
POS System with M-Pesa and WhatsApp API in Kenya | E.D.A by Exotic Digital Access E.D.A Business Management System · Kenya The Smart POS System

WhatsApp Automations and Context-Aware Chatbots for Modern Businesses Using the E.D.A WhatsApp API System
E.D.A WhatsApp API · Business Communication WhatsApp Automations & Context-Aware Chatbots for Smarter Business Communication Modern businesses compete on speed, experience, and intelligence. The

WhatsApp API Kenya: Bulk Messaging, Automation, CRM Integration, and Customer Communication with E.D.A WhatsApp API System
WhatsApp API Kenya | E.D.A Business Messaging System by Exotic Digital Access Exotic Digital Access · Messaging Platform Transform Business Communication with WhatsApp API Kenya

The Ultimate Guide to Choosing the Best POS System in Kenya for SMEs, Retail Shops, Restaurants, Supermarkets, Pharmacies, and Growing Businesses
Best POS System in Kenya | E.D.A by Exotic Digital Access E.D.A by Exotic Digital Access · Kenya How the Best POS System in Kenya

Tech Support Services for Businesses in Kenya: Keeping Modern Businesses Running Smoothly
Tech Support Services for Businesses in Kenya | Exotic Digital Access Exotic Digital Access · IT Support Services Reliable Tech Support Services for Businesses in

Technology Assessment and Optimization Services in Kenya: Building Smarter, Faster, and More Resilient IT Systems
Technology Assessment and Optimization Services | Exotic Digital Access Exotic Digital Access · IT Services Building Smarter, Faster & More Resilient IT Systems with Technology

Web Development and Systems as a Service for SMEs
Web Development and Systems as a Service for SMEs in Kenya | Exotic Digital Access Exotic Digital Access · Digital Transformation Series Web Development and

POS System for SMEs in Kenya Transforming Small Businesses
POS System for SMEs in Kenya | Exotic Digital Access Exotic Digital Access · SME Growth Series How a POS System for SMEs in Kenya

Best POS Systems in Kenya | Fast Sales, Stock & M-Pesa Ready
POS Systems in Kenya | Exotic Digital Access Exotic Digital Access · Kenya The Best POS Systems in Kenyato Grow Your Business Faster Fast billing.
