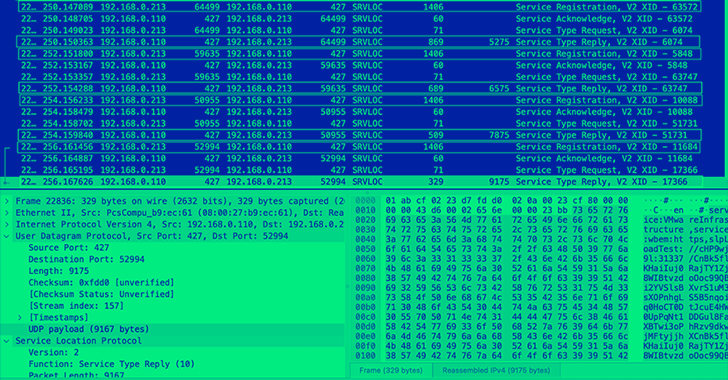
Apr 25, 2023Ravie LakshmananNetwork Security / DDoS Details have emerged about a high-severity security vulnerability impacting Service Location Protocol (SLP) that could be weaponized to launch volumetric denial-of-service attacks against targets. “Attackers exploiting this vulnerability could leverage vulnerable instances to launch massive Denial-of-Service (DoS) amplification attacks with a factor as high as 2200 times, potentially […]
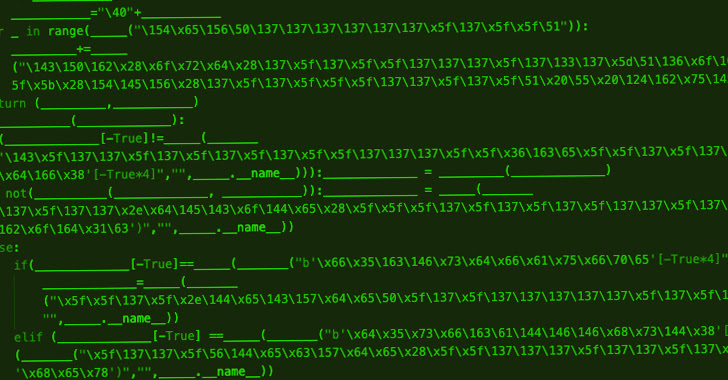
Hackers Exploiting Remote Desktop Software Flaws to Deploy PlugX Malware
Mar 09, 2023Ravie LakshmananThreat Intelligence / Malware Security vulnerabilities in remote desktop programs such as Sunlogin and AweSun are being exploited by threat actors to deploy the PlugX malware. AhnLab Security Emergency Response Center (ASEC), in a new analysis, said it marks the continued abuse of the flaws to deliver a variety of payloads on […]